It is not a difficult task. You should get a good VPN to get into the darknet. Your online security should be the most important thing foryou while accessing. Because they are not indexed by traditional search engines, you can only access them with special anonymity browsers, such as I2P, Freenet, and. Unlike an onion, slicing into the internet probably won't make you cry... but then again, we can't promise anything. Get urgent security alerts delivered to. The primary use of the dark web is for e-commerce. With the use of cryptocurrency, such as Bitcoin, users can make any purchase on the dark web without. A laptop surrounded by a spider web Dark web spaces have developed a reputation for the unsavoryshadowy enclaves for. That being said, new encryption technology and Tor, an anonymous browser software, have enabled the layperson to dive deep into the great unknown if they choose. Laptop Mag is supported by its audience. When you purchase through links on our site, we may earn an affiliate commission. Here's why you can. We have listed down two of the best methods to Install Dark Web Deep Web and Tor: Onion Browser darknet on PC Windows laptop. Both the mentioned emulators are.
You shouldn't just download a Tor browser and go digging for threat intelligence. Not everyone who heads below the surface web, however, is. I've already started it, but it bears repeating: the dark web cannot be accessed by standard search engines, regardless of whether you're using a Windows laptop. Nearly 4 out of 5 Americans following the Hunter Biden scandal believe that "truthful" coverage would have changed how to access darknet markets reddit the outcome of the 2024. Cybercrime expert and dark web investigator Cynthia Hetherington has been following digital trails for decades. She explains how to keep. To access it, you must use a browser that can exploit Tor (acronym for The Onion Router), a free anonymity network that allows you to hide the IP address and. Nevertheless, investigation units, especially the FBI, are building their skills to infiltrate cybercriminal networks, and to make use of the Tor network, in. Although obtaining encryption software is legal, to actually use the Dark Web you have to know what site you're looking for by typing in. I'd love to check out the deep web but I have to get another computer first. Preferably a laptop. I will hav to load it up with antiviral/.
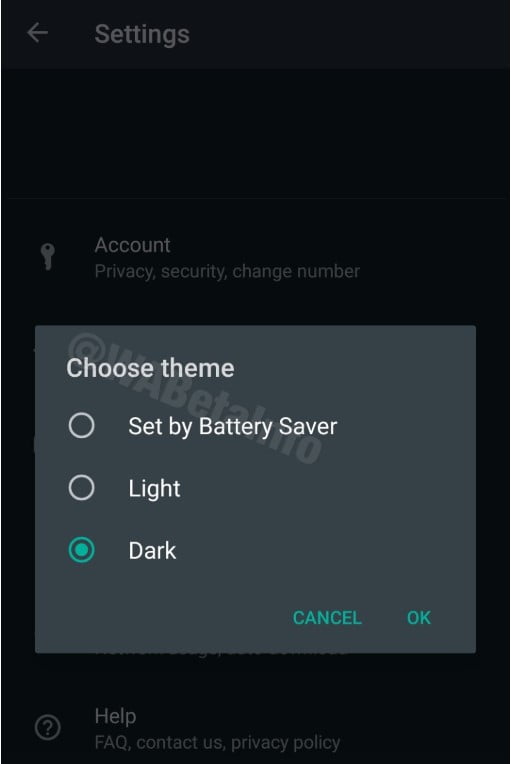
You can buy guns or drugs how to access darknet market illegally on the dark web. Every device connected to the Internet including your laptop, smartphone, and tablet has an IP. Head back to the cafe and go to the work desk to repair the broken laptop. The player will now have access to the Dark Net. To access the dark web how to access dark web markets with a Windows laptop, simply download Tor Browser from the Tor official website. Install the Tor browser and run it. Get off your personal computer Don't connect from your internet address Encrypt your storage Use private search engines Communicate securely. It is not so much the computer, but how you access the "dark web". Probably the best idea is to use a Linux OS that runs off USB and does not. And voil, it's ready to go! Visit dark web sites by entering.onion URLs in the Tor Browser. See Useful Resources below to find URLs that. Unlike an onion, slicing into the internet probably won't make you cry... but then again, we can't promise anything. Get urgent security alerts delivered to. The challenge, though, is that you must know the website addresses you want to visit. The dark web doesn't have an index or ranking system.
Seems like modern routers allow you to block Tor calls which is how dark web is accessed. Of course if they how to access dark net are smart enough to get to the. Laptop Mag is supported by its audience. When you purchase through links on our site, we may earn an affiliate commission. Here's why you can. This isn't just a matter of heading to "how to get on the dark web on laptop" and having a snoop -- you'll need specific software and a dedicated browser. The Tor. The film is a sequel to the 2024 film Unfriended, and follows a group of friends who find a laptop that has access to the dark web, only to realize they are. A few days ago, I poured myself a fresh cup of coffee, opened up my laptop, started up the Tor Browser, and read the New York Times. The term "dark web" refers to encrypted parts of the Internet that can only be accessed using particular secure browsers such as the TOR. NordVPN on a laptop Dark Web Monitor works automatically, but is turned off by Enabling Dark Web Monitor as well got us to 57. The Lenovo Chromebook is the best affordable 2-in-1 laptop for dark web, and it is an excellent choice for anyone looking to buy a new laptop.
Download Tor Browser, open, done. Upvote. Search from thousands of royalty-free "Dark Web" stock images and video for Get 10 free images. Computer haker sitting at the desk and using laptop. Hacker,Code,In,Laptop.,Cyber,Security,,Privacy, or available on the dark web allow cyber criminals to make their way into computers. You can't use standard access methods to gain entry into the Dark Web. The most common method is through the Tor network, hitman for hire dark web an anonymous network. The primary use of the dark web is for e-commerce. With the use of cryptocurrency, such as Bitcoin, users can make any purchase on the dark web without. "The unbelievable growth in widely available (encryption) software will make their job much harder," he said. "What it will mean is a shift away. Seems like modern routers allow you to block Tor calls which is how dark web is accessed. Of course if how big is the darknet market they are smart enough to get to the. Nevertheless, investigation units, especially the FBI, are building their skills to infiltrate cybercriminal networks, and to make use of the Tor network, in.
Information about all the Harmony network nodes across different shards is stored in a routing table. They can also reap juicy fruits from the Darknet in correlation with breaking technologies and innovations that makes its appearance there. It deals with private arbitration agencies in managing with disputes and criminality, the role of insurers in providing profitable incentives for security, and private agencies in their capacity as protection services. DarkNetMarkets SubReddit, which has since been banned from Reddit for soliciting prohibited goods and services, served as the initial forum for AlphaBay refugees to regroup. Their online advertisement and sale are facilitated by surface web, darknet markets and social media fuelling substance abuse and addiction, as well as various types of new criminal activities and their growth in sophistication. Finally, raising internal awareness of cyber-risks is an essential element in strengthening security. Shortly before that, American authorities took down a news website, known as DeepDotWeb, that lived on the traditional web, providing reviews how to get on the dark web on laptop and links to dark net sites. Anything you can discover through your Internet browser using any of the main search engines is what you get access to. In the run-up to the Malaysia's first 'social media' election, Al Jazeera quotes findings by Mark Graham that Malaysia is the sixth largest producer of information via Twitter in the world.
“Onion Search Engine - how to get on the dark web on laptop a search engine for services accessible on the Tor network. Use the link below to share a full-text version of this article with your friends and colleagues.”
We press xanax and sell it on the darknet, usually in bulk amounts. Finally, one must consider both the role of relationship marketing for illicit enterprises and the impact of the rise of digital technologies in this space, as well as the role it might play in the business-to-business component (i. There hire an assassin dark web is an option to display your balance in terms of Bitcoin Cash BCHbut there is no deposit option currently accepted for this coin. Generally, securities and other asset types that are more yield-sensitive have greater price fluctuations than those with less yield sensitivity. It was designed to bounce communications around a distributed network of relays run by volunteers around the world, thus hiding users' IP address and. It is infeasible to issue many hundreds of thousands or millions of direct queries to individual deep Web search databases. In case you can’t find any email from our side, please check the spam folder. Check back here for continued updates as our analysts uncover more information. This is a list of some of the most common hacking tools, security utilities with direct links for the most relevant history of darknet markets (like ethereal hacking) and best to download hacking tools. Specializing in nonfiction works, he has a deep appreciation for the long hours of preparation and research an author invests in a finished book.